Via: CyberCIEGE – A Computer Network Security Video Game
Entropic Memes has recently published CyberCIEGE Revisited and this is the most exciting gameplay debriefing one could possibly have.
Here are the excerpts (and my subsequent review):
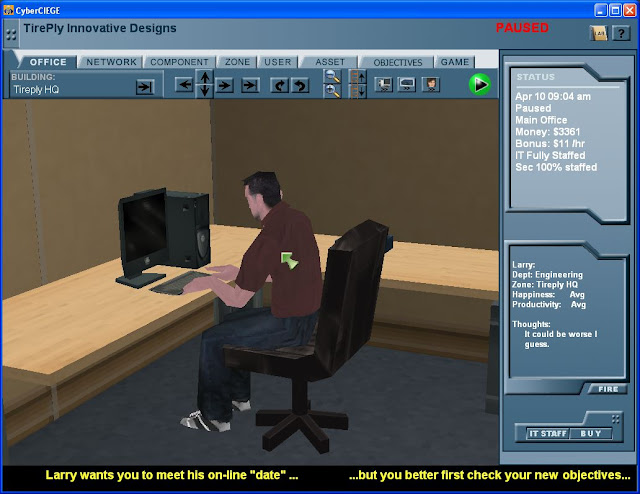
“Basically, CyberCIEGE is kind of like The Sims… only instead of a fit, athletic suburbanite, you get to play a systems administrator, and instead of going shopping and skiing and all those other fun things, you get to, you have to administer and oversee physical and electronic security at your place of employment.”
“To make things challenging, you generally get about a third the budget you would ideally want, and your office is inevitably targeted by every hacker, script kiddie, and foreign special agent in the world - constantly. And, to make things interesting, you get no help from your coworkers - Human Resources seems unable to hire anyone who isn’t working for a foreign intelligence service, and guards - if and when your facility has them - let just about anyone wander around the building, doing all sorts of nefarious things to computers under your control.”
“Put another way, CyberCIEGE is an incredibly difficult security simulation targeted at military and government network managers, and one which promotes one of the most unbelievably stringent security policies in the world. Now, it’s not necessarily an accurate representation of any specific military or government computer security policy, and it doesn’t try to be. What it is, and what it does very well at, is a tool to teach a security mindset - a mindset founded on Murphy’s Law.”
“Put another way, CyberCIEGE is an incredibly difficult security simulation targeted at military and government network managers, and one which promotes one of the most unbelievably stringent security policies in the world. Now, it’s not necessarily an accurate representation of any specific military or government computer security policy, and it doesn’t try to be. What it is, and what it does very well at, is a tool to teach a security mindset - a mindset founded on Murphy’s Law.”
“One of the most valuable aspects of CyberCIEGE - and one which is, as far as I’m aware, unique among security training materials - is that while a lot of the threats and scenarios are undoubtedly exaggerated, sometimes almost ridiculously so, they teach quite a bit about information assurance - network security - in an appreciable, accessible form. Yes, it’s a sandbox environment, but it manages to drive home its points by making them reasonably tangible, rather than mere abstractions. Actions - including inaction - have consequences, and after your third, fourth, or twentieth abject failure, you start to pick up on subtle nuances like this.”
“CyberCIEGE, I want to make it clear, is ridiculously challenging, in large part because it adheres rigorously to - and tries extremely hard to teach and instill - a very, very high set of standards. How hard is it? Well, if Bruce Schneier were running through CyberCIEGE with his right hand, coding Perl with his left, doing Sudoku - in hexadecimal - with his right foot, and drawing Mandelbrot fractals with a set of colored markers clenched between the toes of his left foot - which, aside from using CyberCIEGE, is kind of how I figure Mr. Schneier relaxes of an evening - about a third of the way through the program, he’d probably have to give up on the fractal-drawing; two thirds of the way through, he’d probably have to put down the Sudoku, as well.”
Have I piqued your interest, yet?
The game is freely available to the U.S. Government and a no-cost license is available for educational institutions.
You may also click here to download the free evaluation copy.
“CyberCIEGE, I want to make it clear, is ridiculously challenging, in large part because it adheres rigorously to - and tries extremely hard to teach and instill - a very, very high set of standards. How hard is it? Well, if Bruce Schneier were running through CyberCIEGE with his right hand, coding Perl with his left, doing Sudoku - in hexadecimal - with his right foot, and drawing Mandelbrot fractals with a set of colored markers clenched between the toes of his left foot - which, aside from using CyberCIEGE, is kind of how I figure Mr. Schneier relaxes of an evening - about a third of the way through the program, he’d probably have to give up on the fractal-drawing; two thirds of the way through, he’d probably have to put down the Sudoku, as well.”
Have I piqued your interest, yet?
The game is freely available to the U.S. Government and a no-cost license is available for educational institutions.
You may also click here to download the free evaluation copy.
Game Development
CyberCIEGE is a Serious Game designed to teach network security concepts.
It was created by The Center for Information Systems Security Studies and Research (CISR) at the Naval Postgraduate School (NPS) and Rivermind, Inc.
Development of CyberCIEGE was sponsored by the US Navy, the Naval Education and Training Command, ONR, FAA, and OSD, and it is used as a training tool by agencies of the U.S. government, universities and community colleges.
Numerous NPS (Naval Postgraduate School) students have participated in tool and scenario development.
The game has tremendous potential for use in cyber security training and awareness as well as for more advanced education.
NPS is seeking partners in education to help identify and obtain sponsorship for enhancements to target the game to this new audience.
Players Build Virtual Networks
The game allows users to access assets to achieve their goals and make money for the enterprise while protecting assets from attacks by vandals and professionals
Players purchase and configure computers and network devices to keep demanding users happy (e.g., by providing Internet access) all while protecting assets from a variety of attacks.
Virtual Attackers Motivated by Asset Value
Break in and steal computers, bribe users, distribute Trojan horses and plant trap doors.
Gameplay
- Simulated resource management
- Variety of scenarios
More advanced scenarios cover significant aspects of network management and defense. Players make trade-offs and prioritization decisions as they struggle to maintain a balance between budget, productivity, and security. Players must keep the virtual world’s personnel happy (e.g., by providing Internet access) while protecting assets from vandals and professional attacks.
- Complex network security architectures
- Scenarios divided into multiple phases
The game is designed as a "constructive simulation" set in a three dimensional virtual world. Players build networks and observe virtual users and their thoughts. The game engine incorporates triggers and conditions to allow the scenario designer to provide players with feedback.
- Scenarios builder
A "Scenario Development Kit" is available for creating and customizing scenarios.